How Managed IT Solutions Can Improve Your Company's Cybersecurity and Safeguard Sensitive Data From Hazards
In today's digital landscape, the protection of sensitive information is critical for any organization. Exploring this more reveals important understandings that can considerably affect your company's safety and security position.
Comprehending Managed IT Solutions

The core ideology behind handled IT solutions is the change from reactive analytical to aggressive administration. By outsourcing IT responsibilities to specialized carriers, businesses can concentrate on their core expertises while ensuring that their modern technology facilities is efficiently maintained. This not just improves operational performance yet additionally cultivates innovation, as organizations can designate sources towards tactical efforts instead of day-to-day IT upkeep.
In addition, managed IT solutions promote scalability, enabling companies to adjust to altering organization needs without the problem of substantial in-house IT financial investments. In an age where information stability and system dependability are critical, understanding and applying handled IT services is crucial for organizations seeking to utilize technology properly while protecting their functional continuity.
Secret Cybersecurity Benefits
Handled IT services not just improve functional performance yet also play an essential function in enhancing an organization's cybersecurity posture. Among the main benefits is the establishment of a durable safety and security framework customized to particular organization requirements. Managed IT. These remedies often include thorough danger analyses, permitting companies to identify vulnerabilities and resolve them proactively
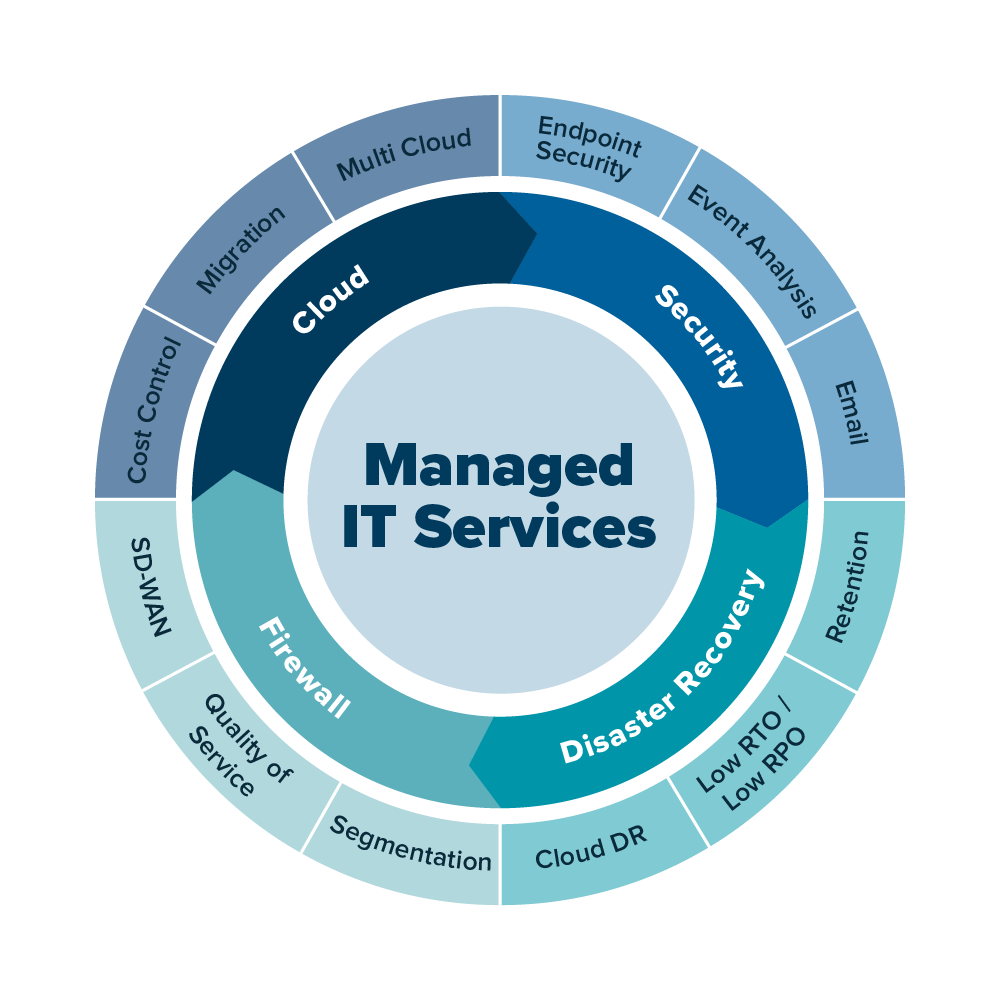
An additional secret advantage is the integration of advanced security innovations, such as firewall softwares, breach detection systems, and encryption procedures. These devices function in tandem to create numerous layers of safety and security, making it dramatically a lot more challenging for cybercriminals to permeate the company's defenses.
Finally, by outsourcing IT administration, business can assign sources much more successfully, enabling interior teams to concentrate on calculated efforts while making sure that cybersecurity remains a top priority. This holistic strategy to cybersecurity eventually safeguards sensitive data and strengthens total service integrity.
Positive Risk Detection
A reliable cybersecurity method hinges on proactive risk discovery, which allows companies to recognize and alleviate prospective risks prior to they rise right into significant cases. Applying real-time tracking options allows companies to track network activity constantly, providing understandings right into anomalies that might indicate a breach. By utilizing sophisticated algorithms and maker knowing, these systems can identify between regular actions and potential threats, allowing for quick action.
Normal vulnerability analyses are an additional vital part of positive danger detection. These analyses aid companies determine weaknesses in their systems and applications, allowing them to remediate susceptabilities prior to they can be exploited by cybercriminals. Furthermore, hazard intelligence feeds play a vital duty in maintaining companies notified about arising threats, enabling them to adjust their defenses appropriately.
Employee training is also essential in promoting a society of cybersecurity understanding. By equipping personnel with the knowledge to acknowledge phishing efforts and various other social design methods, organizations can reduce the likelihood of effective strikes (MSP). Inevitably, a proactive method to danger discovery not only enhances a company's cybersecurity stance yet also imparts confidence among stakeholders that delicate information is being appropriately protected against developing hazards
Tailored Safety Approaches
How can companies properly safeguard their special properties in an ever-evolving cyber landscape? The answer depends on the execution of customized safety and security approaches that align with particular service demands and risk profiles. Acknowledging that no 2 companies are alike, managed IT remedies offer a tailored approach, guaranteeing that protection steps attend to the unique vulnerabilities and functional demands of each entity.
A tailored safety and security strategy starts with an extensive risk assessment, recognizing crucial properties, potential risks, and existing vulnerabilities. This evaluation makes it possible for companies to prioritize safety and security efforts based on their many pressing requirements. Following this, applying a multi-layered safety and security framework ends up being crucial, incorporating innovative technologies such as firewall programs, breach discovery systems, and security procedures tailored to the organization's certain setting.
By constantly examining risk intelligence and adapting security actions, organizations can remain one step in advance of possible strikes. With these personalized approaches, organizations can successfully enhance their cybersecurity position and safeguard sensitive information from arising dangers.
Cost-Effectiveness of Managed Services
Organizations progressively acknowledge the significant cost-effectiveness of managed IT services in today's competitive landscape. By outsourcing IT operates to specialized providers, companies can minimize the expenses related to keeping an internal IT department. This shift makes it possible for companies to allot their resources more efficiently, concentrating on core read what he said business operations while benefiting from expert cybersecurity steps.
Handled IT services generally operate on a registration model, offering foreseeable month-to-month costs that help in budgeting and monetary preparation. This contrasts dramatically with the uncertain costs often related to ad-hoc IT solutions or emergency situation fixings. MSP. Additionally, managed company (MSPs) use accessibility to sophisticated modern technologies and proficient experts that may otherwise be economically out of reach for numerous organizations.
Additionally, the proactive nature of managed solutions aids alleviate the risk of pricey data breaches and downtime, which can cause significant economic losses. By purchasing managed IT solutions, business not only enhance their cybersecurity stance yet also realize long-lasting savings through improved functional performance and reduced threat exposure - Managed IT services. In this way, managed IT services emerge as a critical financial investment that supports both economic security and robust safety

Final Thought
Finally, managed IT services play a pivotal role in enhancing cybersecurity for companies by executing customized safety techniques and constant monitoring. The aggressive discovery of dangers and routine evaluations add to securing sensitive information versus possible violations. In addition, the cost-effectiveness of outsourcing IT management allows companies to focus on their core operations while making certain durable security versus developing cyber hazards. Embracing managed IT options is crucial for maintaining operational connection and data honesty in today's digital landscape.